“Hacked Documents: How Iran Can Track And Control Protesters’ Phones”, The Intercept
Sam Biddle, Murtaza Hussain, October 27 2022
The documents provide an inside look at an Iranian government program that lets authorities monitor and manipulate people’s phones.
AS FURIOUS ANTI-GOVERNMENT protests swept Iran, the authorities retaliated with both brute force and digital repression. Iranian mobile and internet users reported rolling network blackouts, mobile app restrictions, and other disruptions. Many expressed fears that the government can track their activities through their indispensable and ubiquitous smartphones.
Iran’s tight grip on the country’s connection to the global internet has proven an effective tool for suppressing unrest. The lack of clarity about what technological powers are held by the Iranian government — one of the most opaque and isolated in the world — has engendered its own form of quiet terror for prospective dissidents. Protesters have often been left wondering how the government was able to track down their locations or gain access to their private communications — tactics that are frighteningly pervasive but whose mechanisms are virtually unknown.
“This is not a surveillance system but rather a repression and control system to limit the capability of users to dissent or protest.”
While disconnecting broad swaths of the population from the web remains a favored blunt instrument of Iranian state censorship, the government has far more precise, sophisticated tools available as well. Part of Iran’s data clampdown may be explained through the use of a system called “SIAM,” a web program for remotely manipulating cellular connections made available to the Iranian Communications Regulatory Authority. The existence of SIAM and details of how the system works, reported here for the first time, are laid out in a series of internal documents from an Iranian cellular carrier that were obtained by The Intercept.
According to these internal documents, SIAM is a computer system that works behind the scenes of Iranian cellular networks, providing its operators a broad menu of remote commands to alter, disrupt, and monitor how customers use their phones. The tools can slow their data connections to a crawl, break the encryption of phone calls, track the movements of individuals or large groups, and produce detailed metadata summaries of who spoke to whom, when, and where. Such a system could help the government invisibly quash the ongoing protests — or those of tomorrow — an expert who reviewed the SIAM documents told The Intercept.
-
Evidence of Iran’s cyber crackdown is everywhere, but little is known about its methods.
-
A software program imposed on Iranian mobile companies allows the government direct access.
-
SIAM allows mobile operators to track users’ locations and restrict their data usage.
-
A function called “Force2GNumber” targets individual users for slower speeds that are susceptible to surveillance.
“SIAM can control if, where, when, and how users can communicate,” explained Gary Miller, a mobile security researcher and fellow at the University of Toronto’s Citizen Lab. “In this respect, this is not a surveillance system but rather a repression and control system to limit the capability of users to dissent or protest.”
SIAM gives the government’s Communications Regulatory Authority — Iran’s telecommunications regulator — turnkey access to the activities and capabilities of the country’s mobile users. “Based on CRA rules and regulations all telecom operators must provide CRA direct access to their system for query customers information and change their services via web service,” reads an English-language document obtained by The Intercept. (Neither the CRA nor Iran’s mission to the United Nations responded to a requests for comment.)
The SIAM documents are drawn from a trove of internal materials from the Iranian cellular carrier Ariantel, including years of email correspondence and a variety of documents shared between Ariantel employees, outside contractors, and Iranian government personnel. The cache of materials was shared with The Intercept by an individual who claimed to have hacked Ariantel, and believed the documents were in the public interest given the ongoing protests in Iran and the threat SIAM might pose to demonstrators. (Ariantel did not respond to a request for comment.)
The details of the program reported here are drawn largely from two documents contained in the archive. The first is a Persian-language user manual for SIAM that appears to have originated from within the Office of Security of Communications Systems, or OSCS, a subdivision of the CRA. Emails reviewed by The Intercept show that this SIAM manual was sent to Ariantel directly by the CRA and repeatedly forwarded between the mobile carrier’s employees in recent years. The emails show that the CRA and Ariantel discussed SIAM as recently as August. The second document, produced during a proposed deal with a Spanish telecom contractor, is an English-language manual that documents many of the same SIAM capabilities. Miller told The Intercept that the English SIAM manual appeared to be written by a person or people with specialized technical knowledge of mobile networks.
Experts on mobile security and Iranian government censorship say the functionality revealed by the SIAM program poses a clear threat to protesters demonstrating against the government over the past month.
“These functions can lead to life-and-death situations in a country like Iran, where there is no fair judicial process, no accountability, and we have a huge pattern of violations of people’s rights,” said Amir Rashidi, an internet security and digital rights expert focused on Iran. “Using the tools outlined in this manual could not only lead to mass surveillance and violations of privacy — it can also easily be used to identify the location of protesters who are literally risking their lives to fight for their basic rights.”
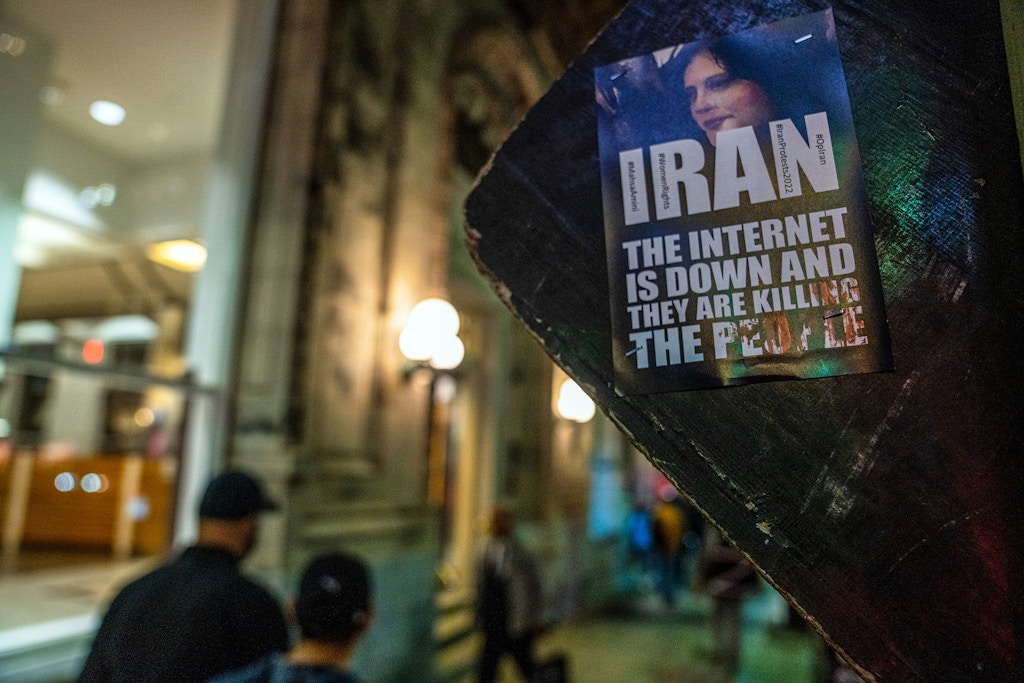
Photo: Katherine Cheng/SOPA/LightRocket via Getty Images
While not directly mentioned in the manuals, downgrading users to a 2G connection could also expose perilously sensitive two-factor authentication codes delivered to users through SMS. The Iranian government has previously attempted to undermine two-factor authentication, including through malware campaigns targeting dissidents.
“Generally speaking, forcing a phone to use the 2G network would still allow the phone to receive a two-factor SMS authentication message because SMS is sent over the mobile signaling network,” explained Miller. “However, the effect of forcing a user onto the 2G network, more importantly, would essentially render the corresponding real-time application services such as P2P communication, social media, and internet useless.”
While current 5G and 4G cellular connections have more robust built-in encryption systems to thwart eavesdropping, the 2G cellular standard, first introduced in 1991, generally does not encrypt data or uses outdated encryption methods that are easy to crack. Law enforcement agencies in the United States have also employed this technique, using hardware like the controversial “stingray” device to create a bogus 2G network blanketing a small area and then trick targeted phones into connecting to it.
Miller pointed out that the target of a 2G downgrade might experience the attack as little more than spotty cell reception. “It can be viewed as a method to appear as if the network is congested and severely limit a user’s data services,” Miller said.
Slowing connectivity is only one of many telecom tools available to Ariantel — and the CRA — that could be used to monitor political dissent. SIAM also provides a range of tools to track the physical locations of cell users, allowing authorities to both follow an individual’s movements and identify everyone present at a given spot. Using the “LocationCustomerList” command allows SIAM operators to see what phone numbers have connected to specified cell towers along with their corresponding IMEI number, a unique string of numbers assigned to every mobile phone in the world. “For example,” Miller said, “if there is a location where a protest is occurring, SIAM can provide all of the phone numbers currently at that location.”
SIAM’s tracking of unique device identifiers means that swapping SIM cards, a common privacy-preserving tactic, may be ineffective in Iran since IMEI numbers persist even with a new SIM, explained a network security researcher who reviewed the manuals and spoke on the condition of anonymity, citing their safety.
SIAM’s location-tracking power is particularly alarming given the high-stakes protests taking place across Iran. The Intercept reviewed undated text messages sent to Iranian mobile phone users from local police in the city of Isfahan informing them that they had been confirmed to have been in a location of “unrest” and warning them not to attend in the future. Many Iranian social media users have reported receiving similar messages in recent weeks, warning them to stay away from the scene of protests or from associating with “anti-revolutionary” opponents of the government online.
Armed with a list of offending phone numbers, SIAM would make it easy for the Iranian government to rapidly drill down to the individual level and pull a vast amount of personal information about a given mobile customer, including where they’ve been and with whom they’ve communicated. According to the manuals, user data accessible through SIAM includes the customer’s father’s name, birth certificate number, nationality, address, employer, billing information, and location history, including a record of Wi-Fi networks and IP addresses from which the user has connected to the internet.
While much of Iran’s surveillance capacity remains shrouded in mystery, details about the SIAM program contained in the Ariantel archive provide a critical window into the types of tools the Iranian government has at its disposal to monitor and control the internet, as it confronts what may be the greatest threat to its rule in decades.
“These documents prove something that we have long suspected, which is that even devices that use encryption for messaging are still vulnerable because of the nature of internet infrastructure in Iran,” said Mahsa Alimardani, a senior researcher with the internet freedom organization Article 19. “Security measures like two-factor identification using text messages still depend on telecommunications companies connected to the state. Average internet users are forced to connect through nodes controlled by these companies, and their centralization of authority with the government makes users vulnerable to insidious types of surveillance and control.”

Photo: Stringer/Anadolu Agency via Getty Images
The CRA is known to play an integral role in filtering Iran’s internet access. In 2013, the agency was among a list of Iranian government entities sanctioned by the U.S. Treasury Department for its role in the “blockage of hundreds of public Internet websites” around the time of the disputed 2009 Iranian presidential election. The agency’s powers are believed to have grown since then, as the Iranian government has embraced the concept of “internet sovereignty” as a means of social control. A report on the November 2019 cyber crackdown by Article 19 found that the shutdowns were carried out in large part by officials from the CRA ordering internet service providers to shut down during the unrest.
The Iranian government has long viewed internet freedom as a national security issue and has taken steps to securitize Iranians’ online access. As in the United States, where the National Security Agency has used government secrecy and legal coercion to turn the telecom and data sectors into intelligence-gathering tools, the Iranian state compels communications networks to give the government access through required hardware and software. In Iran, where the autocratic reach of central government leadership touches nearly every aspect of the state without even superficial democratic oversight, the powers afforded by this integration are far greater and far more draconian in consequence.
Part of this effort has included directly assigning Iranian intelligence personnel to government bodies tasked with internet regulation, like the CRA. The Article 19 report notes the close personnel relationship between the CRA’s OSCS division and Iran’s Ministry of Intelligence.
